Managed IT vs. In-House IT: What Actually Works for Multi-Location Businesses? →
Phishing is a term that describes emails that look legitimate but are actually designed to fool users into revealing personal information such as passwords, bank account numbers, etc. Phishing (the […]
Phishing is a term that describes emails that look legitimate but are actually designed to fool users into revealing personal information such as passwords, bank account numbers, etc. Phishing (the […]

“Password1”, “Password2”, “Password3”, or the ever-popular and bullet-proof “Password123”. Sometimes you even get fancy and add an exclamation point to the end (when forced to). Are any of these ringing […]

[youtube https://www.youtube.com/watch?v=yUf60OwiE8U] Cybersecurity training is here! Talk to us about our employee training program that trains your employees to identify cybersecurity threats to your business, your...

[img src=”/wp-content/uploads/2018/05/old-lynksys-router_1.jpg”] We get a lot of questions about the latest router malware attacks, so we created a video to address your concerns. If you have a home class...

We had a packed house today at the Alamance County Chamber of Commerce for the Cybersecurity Lunch and Learn. Mike Farlow with ComTech provided great information on current Cybersecurity issues […]
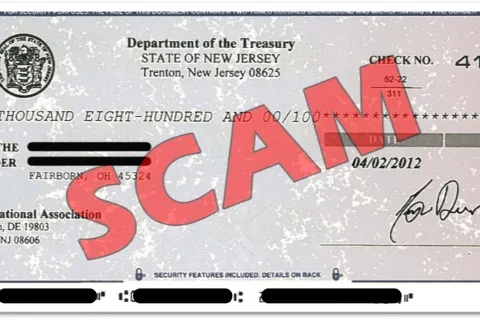
A new scam has emerged that can put your hard earned money at risk. Fake check scams are becoming more common as they leverage payment as a bait to lure […]

I get this question quite often and rightfully so. There are many ways to purchase Office and they can be confusing. Depending upon your situation one method may be better […]

Power jacks in public places can be dangerous. Learn how to protect yourself against “juice jacking”.

In the interest of brevity, I won’t bother to go into deep detail about the two latest PC threats that have been discovered. Feel free to google “spectre” or “meltdown” […]
How many of you have started this new year off but have brought over A LOT of baggage from 2017 that is weighing you down? How many of you know […]
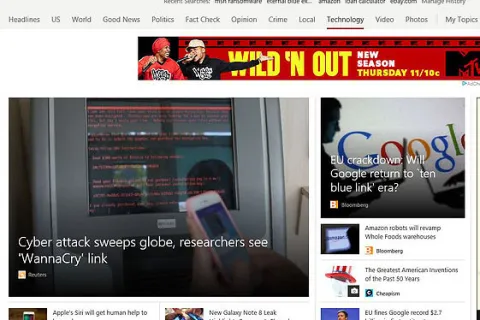
Above is a screenshot from the news on June 28th, 2017. It is a common headline lately. Although ransomware is devious and disruptive to business, there are some things you […]